Blockchain for Cybersecurity represents a significant paradigm shift in how we protect digital information from malicious attacks. As major organizations like Lockheed Martin and the US military embrace blockchain technology, the potential for advanced cybersecurity solutions becomes clearer. Unlike traditional centralized systems that leave data vulnerable to breaches, blockchain offers a decentralized security framework that mitigates risks and enhances data breach prevention efforts. This innovative approach not only ensures data integrity but also fosters a high-trust environment for sensitive information exchange. In an era where enterprise security is under constant threat, the adoption of blockchain technology could redefine our defenses against cybercrime.
The intersection of blockchain and digital security introduces a revolutionary way to safeguard information assets. Often referred to as decentralized security, this technology transcends traditional cybersecurity measures by employing distributed ledgers that enhance authenticity and privacy. With an increased focus on securing online transactions, the principles of blockchain align perfectly with the growing demands for more resilient cybersecurity frameworks. By leveraging blockchain’s unique capabilities, organizations can implement robust data protection strategies that resist the evolving landscape of cyber threats. As cybersecurity continues to evolve, the integration of blockchain may well be the key to achieving more effective and reliable systems.
Leveraging Blockchain for Cybersecurity Solutions
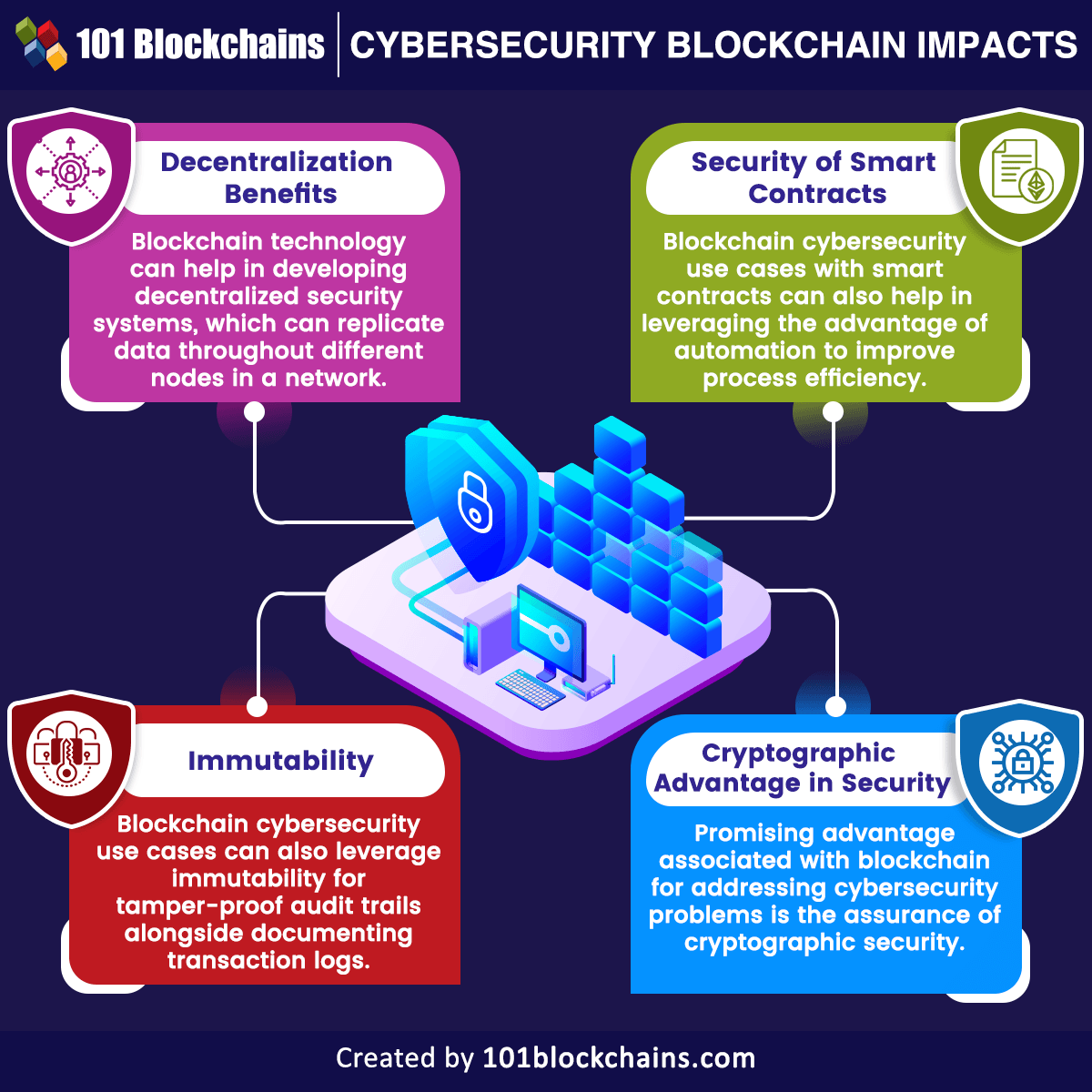
The integration of blockchain into cybersecurity solutions marks a significant advancement in protecting sensitive data. As major corporations and governments adopt blockchain technology, its decentralized nature is proving to be a game-changer in the realm of cybersecurity. Unlike traditional systems that rely on centralized databases, blockchain allows for data to be distributed across multiple nodes. This dispersion significantly reduces the risk of data breaches, as there is no single point of failure that hackers can exploit. By utilizing blockchain for cybersecurity solutions, organizations can fortify their defenses and enhance their overall data integrity.
Moreover, the inherent features of blockchain, such as immutability and transparency, add layers of security that traditional systems simply cannot offer. Each transaction or data entry on the blockchain is time-stamped and encrypted, creating a verifiable audit trail that can help detect unauthorized access or tampering. This capability is particularly crucial in industries like finance and healthcare, where sensitive information must be protected at all costs. Consequently, organizations looking to stay ahead of cyber threats are increasingly recognizing the value of incorporating blockchain technology into their cybersecurity arsenal.
Implementing Blockchain for Data Breach Prevention
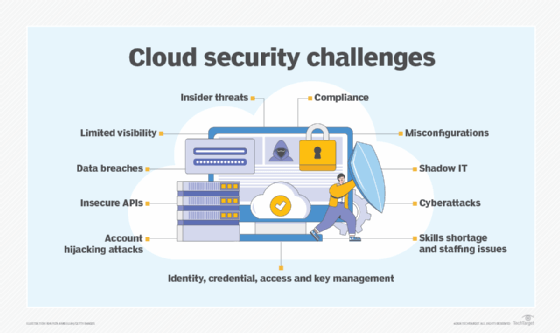
Data breaches remain a top concern for organizations worldwide, with incidents like the Equifax breach underscoring the vulnerabilities of centralized cybersecurity models. By implementing blockchain for data breach prevention, companies can eliminate the dependence on centralized systems, which are prone to attacks. Blockchain technology distributes data across a network, ensuring that even if one node is compromised, the overall integrity of the dataset remains intact. This decentralized approach not only fortifies defenses against intrusions but also enhances the reliability of stored information.
Furthermore, blockchain’s cryptographic principles provide a robust framework for securing data exchanges. Each piece of information added to the blockchain is linked to previous data through advanced encryption methods, making unauthorized alterations easily detectable. For organizations, this means a significant reduction in the risk of data alteration or theft. The proactive nature of blockchain technology ensures compliance with regulations and the protection of customer trust by preserving the confidentiality and integrity of personal information, making it a vital tool for modern cybersecurity strategies.
The Role of Tamper-Free Networks in Cybersecurity
Tamper-free networks are a critical innovation within blockchain technology that significantly enhances cybersecurity. By design, blockchain creates a permanent record of each transaction, linked together cryptographically. This chain of blocks means that any attempt to alter a previous entry would not only be futile but also starkly visible to all network participants. Such transparency acts as a deterrent for cybercriminals who typically exploit weaknesses in traditional systems.
In this context, the tamper-proof nature of blockchain ensures that organizations can maintain accurate and unchangeable records of transactions, critical for auditing and compliance purposes. This advantage is particularly beneficial for sectors dealing with sensitive data, as it fosters trust among stakeholders while providing an additional layer of security. Consequently, adopting tamper-free networks can substantially mitigate risks associated with data fraud and enhance an organization’s cybersecurity posture.
Enhancing Enterprise Security with Blockchain
As enterprise security threats evolve, incorporating blockchain technology offers an innovative solution to these challenges. By leveraging blockchain’s decentralized architecture, businesses can enhance their security measures, minimizing the risks posed by data breaches and cyberattacks. The ability of blockchain to facilitate secure, encrypted transactions without the need for a central authority provides enterprises with a robust framework for safeguarding critical information.
In addition to its decentralized nature, blockchain offers several features essential for enterprise-level security, including smart contracts and distributed ledgers. These components enable organizations to automate and secure business processes, ensuring that data integrity and authenticity are upheld across all transactions. As businesses increasingly recognize the advantages of blockchain, its adoption within enterprise security frameworks is expected to grow, ultimately shaping the future landscape of corporate cybersecurity.
Keyless Signature Infrastructure as a Security Solution
Keyless Signature Infrastructure (KSI) represents a pioneering approach to enhancing cybersecurity through blockchain technology. By eliminating the need for a central repository of public keys, organizations can significantly reduce the attack surface that cybercriminals exploit. Instead of relying on traditional Public Key Infrastructure (PKI), KSI distributes keys among multiple participants, allowing for secure transactions while preserving the integrity of user identities.
This innovative method not only fortifies individual identity management but also strengthens overall data exchange processes. In situations where a breach does occur, the decentralized approach of KSI helps prevent systemic vulnerabilities and maintains the continuity of service. As the cybersecurity landscape evolves, implementing keyless signature infrastructure through blockchain technology will become increasingly critical for organizations aiming to protect sensitive information.
Blockchain: A Trusted Environment for Secure Transactions
Blockchain technology stands out as a mechanism that fosters a trusted environment for secure transactions. By utilizing advanced cryptographic methods, blockchain ensures that all parties can validate transaction authenticity without relying on a third-party intermediary. This shift from traditional trust models to a decentralized ledger approach facilitates safer interactions, as users can be confident in the legitimacy of the data shared among them.
Moreover, the use of shared hash functions in blockchain assures that each transaction is consistently verified by the network, reducing the chances of fraud. For businesses, this creates a powerful ecosystem where trust is embedded in the technological architecture, allowing for smoother transactions and improved partnerships. As blockchain technology continues to evolve, its capacity to create trusted environments will play a pivotal role in reshaping business practices and enhancing security measures across various industries.
User Access Management Enhanced by Blockchain
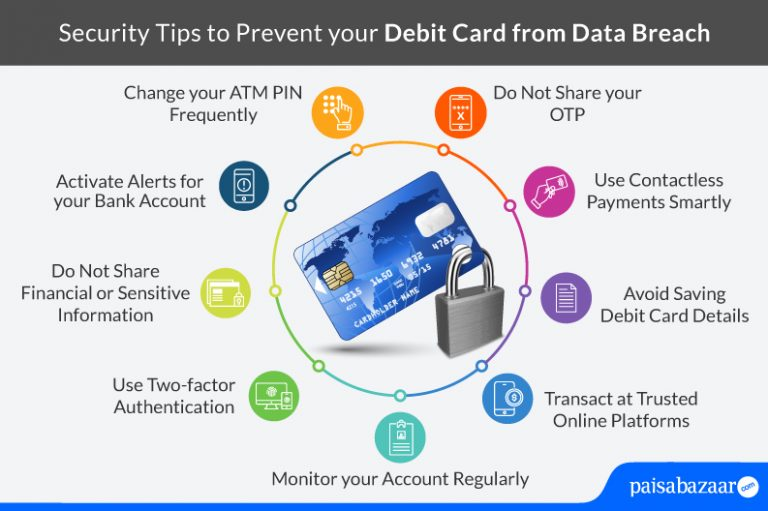
User access management is a critical aspect of cybersecurity, and blockchain technology offers revolutionary enhancements in this area. By linking user identities to unique tamper-proof hashes, organizations can ensure that identity duplication becomes nearly impossible. This secure management of user identities is crucial in protecting sensitive data, as unauthorized access becomes significantly restricted.
In cases where there is a security incident, the ability to restore an identity management system that leverages blockchain’s inherent features expedites recovery processes. Organizations can efficiently track identity paper trails, ensuring compliance and accountability across their security frameworks. As cyber threats continue to escalate, adopting blockchain for user access management will be vital for maintaining robust security protocols.
Blockchain as an Alternative to Traditional Internet Protocols
The limitations of traditional HTTP in terms of security vulnerabilities have prompted the exploration of blockchain as a potential alternative web protocol. The InterPlanetary File System (IPFS) exemplifies this innovative approach, effectively utilizing blockchain principles to create a more security-focused internet. By employing distributed nodes rather than centralized servers, IPFS minimizes risks associated with data breaches, as it does not rely on single points of failure.
Additionally, the use of blockchain in web protocols significantly reduces the necessity for user passwords—a common target for hackers. For instance, the Ukrainian startup REMME provides unique SSL certificates through blockchain, effectively eliminating the need for traditional authentication servers. This advancement not only enhances security by lowering the likelihood of password theft but also reflects a broader transition toward more resilient internet frameworks driven by blockchain technology.
The Future of Cybersecurity: Blockchain Adoption Trends
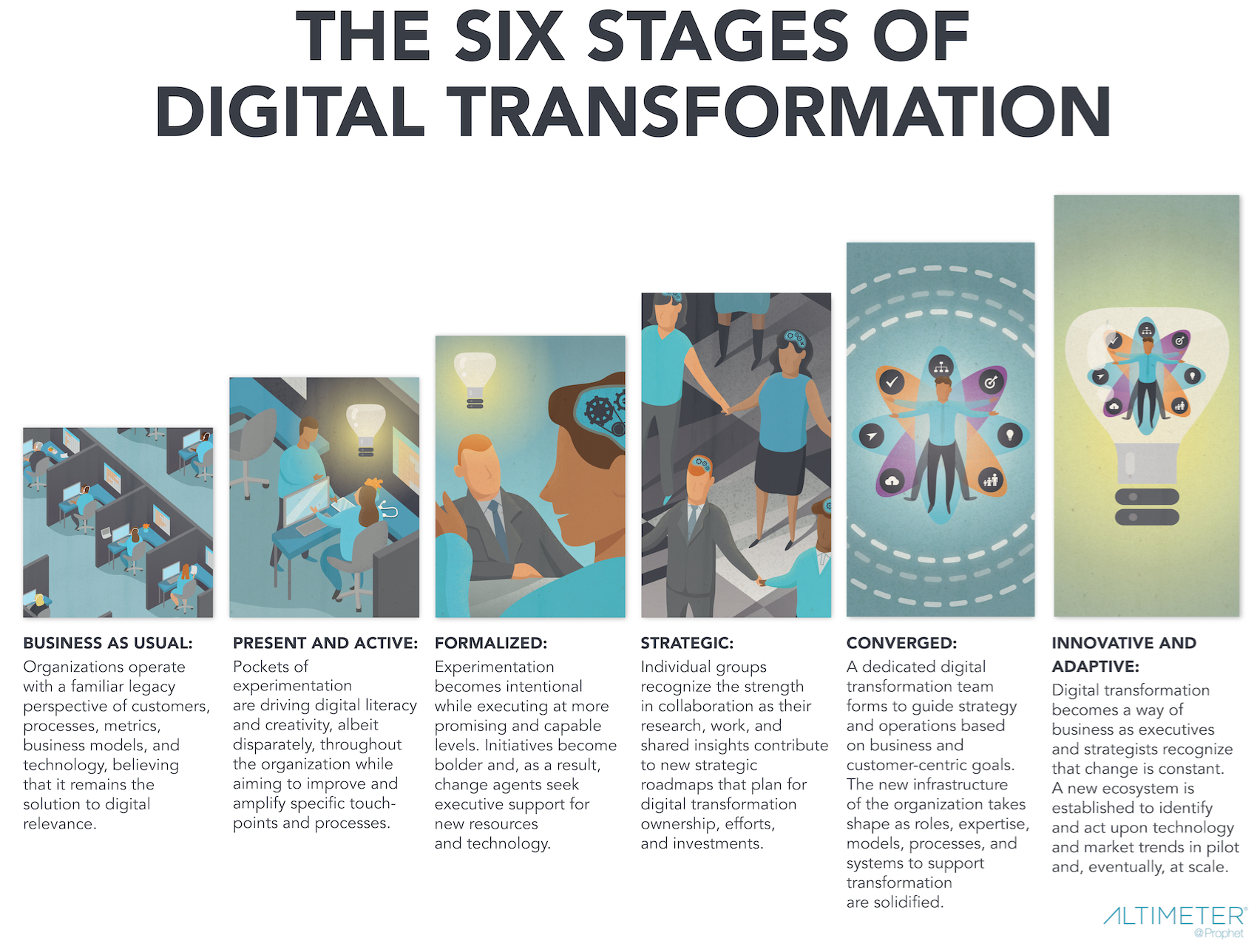
The future of cybersecurity is poised for transformation as the adoption of blockchain technology gains momentum across various sectors. Industry experts predict that the cybersecurity market will reach unprecedented levels, fueled by blockchain’s ability to deliver decentralized security solutions. Analysts estimate that the market will exceed $80 billion, underscoring the relevance of blockchain in modern security frameworks.
Despite its promising benefits, experts highlight that widespread adoption may face hurdles, particularly in regions such as India. However, as organizations increasingly recognize the effectiveness of blockchain-based solutions, particularly in data protection and privacy, the technology’s integration into enterprise security models is likely to accelerate. Companies that embrace blockchain capabilities will not only reinforce their defenses but also position themselves as leaders in the rapidly evolving cybersecurity landscape.
Frequently Asked Questions
What are the benefits of using blockchain technology for cybersecurity solutions?
Using blockchain technology for cybersecurity solutions offers numerous benefits, including enhanced data integrity, decentralized security, and improved data breach prevention. Unlike traditional centralized models, blockchain creates a tamper-proof environment where data is stored across multiple nodes, reducing the risk of a single point of failure and providing a more resilient and secure framework for enterprises.
How does blockchain technology improve data breach prevention?
Blockchain technology improves data breach prevention by employing a decentralized security model that eliminates the risks associated with centralized data storage. Each block in the blockchain is encrypted and connected to the previous one, making it nearly impossible for hackers to alter data without detection. This unique design ensures that even if one node is compromised, the integrity of the entire network remains intact, offering robust protection against cyber threats.
What role does decentralized security play in enterprise security with blockchain?
Decentralized security plays a crucial role in enhancing enterprise security with blockchain by distributing data across a network of computers rather than storing it in a single location. This approach minimizes the potential impact of cyberattacks, as compromising one node does not lead to a catastrophic data breach. Instead, the integrity and availability of the data are maintained across the decentralized network, reinforcing the overall security posture of enterprises.
How can blockchain assist in creating a trusted environment for cybersecurity?
Blockchain assists in creating a trusted environment for cybersecurity by utilizing advanced cryptography to secure interactions between users. The decentralized nature of blockchain eliminates the need for blind trust in third parties, allowing users to confidently transact with each other. As users can verify their identities through tamper-proof hashes, the reliability and security of data exchanges are significantly enhanced.
What is the keyless signature infrastructure (KSI), and how does it benefit cybersecurity?
Keyless Signature Infrastructure (KSI) is a blockchain-based system that securely manages public keys without the traditional vulnerabilities of central repositories. By distributing public keys across the blockchain, KSI reduces the risk of breaches and forgery typically associated with centralized public key infrastructures. This technology ensures that digital identity verification is both secure and reliable, making it a vital component in modern cybersecurity solutions.
How does blockchain technology prevent unauthorized access in user access management?
In user access management, blockchain technology prevents unauthorized access by linking a user’s identity to a unique, tamper-proof hash. This means that duplicating or falsifying identities becomes extremely difficult. If an incident occurs, the blockchain can be referenced to restore the affected identity management system, significantly enhancing security against identity fraud.
Can blockchain be effectively implemented as an alternative to traditional web protocols for cybersecurity?
Yes, blockchain can be effectively implemented as an alternative to traditional web protocols, such as HTTP. Technologies like the InterPlanetary File System (IPFS) utilize blockchain principles to create a decentralized web environment. This mitigates the risks associated with central points of failure and user password vulnerabilities, making web interactions more secure.
What impact does blockchain adoption have on the future of enterprise cybersecurity?
The adoption of blockchain technology is poised to significantly impact the future of enterprise cybersecurity by introducing innovative security measures such as encrypted authentication, smart contracts, and distributed ledgers. As businesses begin to integrate these solutions, the cybersecurity market is expected to grow, offering enhanced protection against cyber threats and fostering trust in digital transactions.
| Key Components of Blockchain for Cybersecurity | Description | Benefits | |
|---|---|---|---|
| Decentralized Security Model | Removes risks associated with single point breaches inherent in centralized systems. | ||
| Tamper-Free Network | Changes to any block can be easily identified and flagged, making alterations nearly impossible. | ||
| Keyless Signature Infrastructure | Enhances public key management and reduces the risk of identity fraud. | ||
| Trusted Environment | Enables secure transactions without the need for third-party trust. | ||
| User Access Management | Links user identity to a tamper-proof hash for enhanced security. | ||
| Alternative to HTTP | Provides a decentralized web structure that reduces data breach risks by eliminating central points of control. | ||
| Enterprise Security Adoption | Encourages businesses to adopt more secure cybersecurity solutions through technologies such as distributed ledgers and smart contracts. | ||
Summary
Blockchain for Cybersecurity is revolutionizing the way sensitive data is secured and managed. Major corporations and governments around the world are turning to blockchain technology to create more resilient systems that can withstand cyber attacks. By employing a decentralized approach, blockchain not only ensures data integrity but also minimizes the risk of breaches. As the technology continues to develop, its applications in cybersecurity are likely to expand, providing enhanced safety for businesses and users alike.