Cybersecurity has swiftly emerged as a vital priority for organizations around the globe, with Chief Information Security Officers (CISOs) increasingly vigilant against a myriad of cyber threats. In today’s digital age, where nearly half a million attacks occur every minute, the necessity for robust defenses against ransomware attacks and vulnerabilities in cloud security has never been more pressing. As technology advances rapidly, it presents both opportunities and challenges that demand innovative solutions to safeguard digital assets. Furthermore, the rising prominence of women in technology is reshaping the cybersecurity landscape, as they lead efforts in developing cutting-edge tools and firewalls. Their contributions not only enhance security frameworks but also inspire a more inclusive tech environment that promises a stronger defense against evolving cyber threats.
The realm of digital security is constantly evolving, with safeguarding information and data integrity becoming paramount in contemporary society. Experts in information protection, such as Chief Security Officers (CSOs) and cybersecurity risk managers, are tasked with identifying and mitigating potential threats to organizations. As cybercriminals devise new strategies, including sophisticated ransomware schemes, the focus on comprehensive cloud defenses is critical. Additionally, there is a growing recognition of the importance of diverse perspectives in technology, particularly from women who are making strides in this field. The integration of emerging talent not only fortifies defenses but also paves the way for innovative practices in the protection of digital space.
Understanding the Role of CISOs in Cybersecurity
In today’s fast-paced digital environment, Chief Information Security Officers (CISOs) play a crucial role in safeguarding organizational assets from cyber threats. As the landscape of cybersecurity evolves, CISOs are required to stay ahead of emerging technologies and threats. They must navigate the complexities of protecting sensitive data while ensuring business continuity. With the increasing number of cyber attacks, the pressure on CISOs to prioritize network security has never been greater, making their position vital in establishing a strong cybersecurity framework.
Moreover, the responsibilities of CISOs have expanded beyond mere compliance and risk management. They now must lead their teams in implementing advanced security measures, including threat intelligence, incident response strategies, and continuous monitoring. By fostering a culture of security awareness among employees, CISOs can mitigate human errors that often serve as the weakest links in cybersecurity. Their leadership is essential in aligning security initiatives with overall business objectives to defend against sophisticated attacks.
The Rise of Ransomware Attacks in Today’s Digital Landscape
Ransomware attacks have emerged as one of the most prevalent cyber threats in recent years, causing immense disruption to organizations across various sectors. These attacks, which often involve encrypting an organization’s data and demanding a ransom for its release, have grown more sophisticated and targeted. As businesses increasingly rely on digital platforms, the potential impact of ransomware is magnified, reinforcing the need for robust cybersecurity measures. Organizations must develop comprehensive incident response plans and regularly update their security infrastructure to combat the ever-evolving tactics employed by cybercriminals.
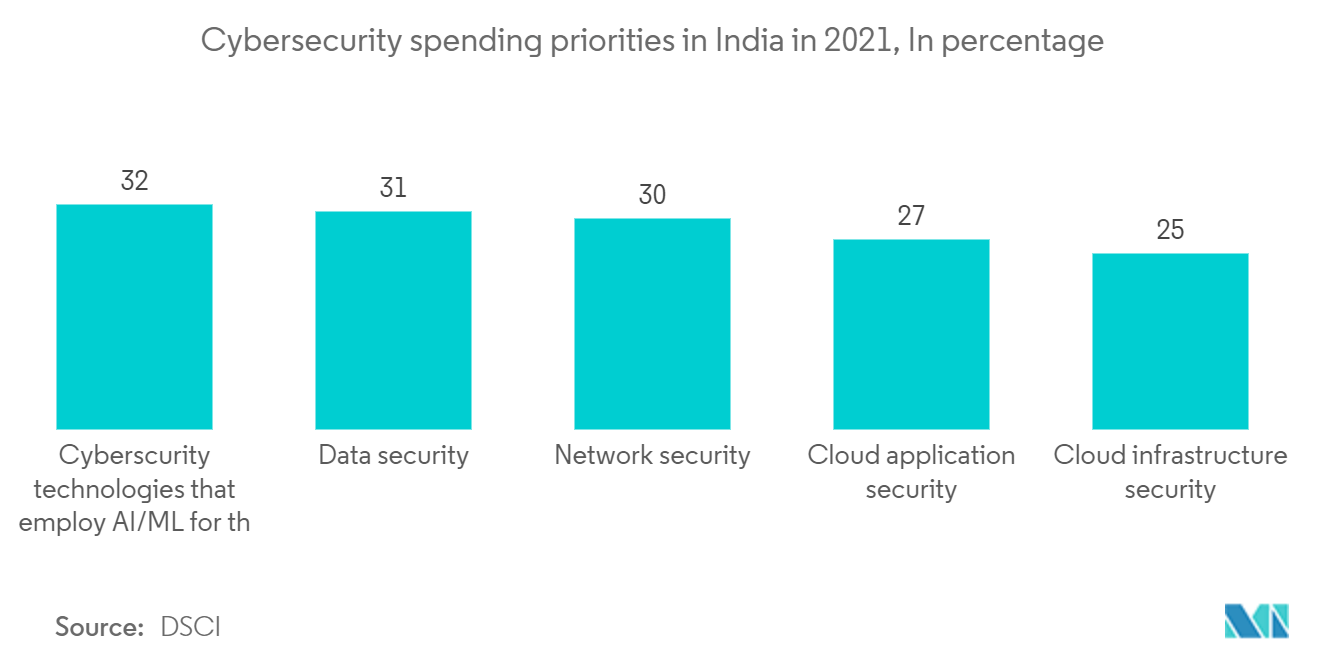
In response to this alarming trend, companies are investing in cybersecurity solutions that incorporate artificial intelligence and machine learning to detect potential ransomware activity before it causes harm. Moreover, organizations are emphasizing employee training programs to educate staff on recognizing phishing attempts and suspicious activities that could lead to ransomware infiltration. By proactively addressing these threats, businesses can not only protect their assets but also maintain customer trust and credibility in an age where cyber threats are ever-present.
Cloud Security: Importance and Best Practices
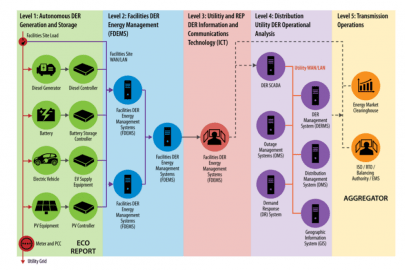
As organizations continue to migrate to cloud-based services, the importance of cloud security becomes increasingly clear. The flexibility and scalability offered by cloud solutions come with a unique set of vulnerabilities that can expose sensitive data to cyber threats. It is critical for Chief Information Security Officers (CISOs) to implement best practices for cloud security, including data encryption, access controls, and regular security assessments. By understanding the shared responsibility model of cloud security, businesses can better mitigate risks associated with data breaches.
Furthermore, comprehensive training and development of cybersecurity portfolios are essential for organizations leveraging cloud technology. As noted by cybersecurity experts, fostering collaboration between IT teams and cybersecurity professionals can enhance security posture during cloud integration. Continuous monitoring and securing data at every phase of its lifecycle, from creation to deletion, are non-negotiable practices. Organizations must remain vigilant and adapt their security measures as they embrace the advantages of cloud computing.
Women in Technology: Leading the Charge in Cybersecurity
The growing presence of women in technology is transforming the cybersecurity landscape. Female leaders in the field bring innovative approaches to tackling complex security challenges, paving the way for a more diverse and inclusive technology environment. As female experts, like Jamuna Swamy and Lopa Mudraa Basuu, share their insights, they inspire a new generation of women to pursue careers in cybersecurity. Their success stories highlight the critical need for diversity in a field that traditionally lacks representation, demonstrating that women can excel in roles traditionally dominated by men.
Moreover, women’s contributions to cybersecurity extend beyond leadership; they are actively designing and implementing security policies that address vulnerabilities and counteract emerging threats. By fostering an inclusive culture, organizations can not only attract top talent but also enhance their cybersecurity strategies. Embracing the perspectives and experiences of women in technology leads to more robust security solutions and ultimately a safer digital ecosystem.
Addressing Internal Threats in Cybersecurity
Internal threats remain a significant concern within the realm of cybersecurity. Unlike external attackers, internal threats often arise from employees who may unintentionally or maliciously compromise sensitive data. It is crucial for organizations to recognize that their own workforce can pose risks, either through lack of awareness or discontent. This calls for a multi-faceted approach to mitigate internal threats, including regular employee training, strict access controls, and a transparent reporting process for suspicious activities.
CISOs must implement a culture of accountability and vigilance among staff members to ensure that everyone plays a role in maintaining cybersecurity. Regular audits and monitoring of user access can help identify potential vulnerabilities introduced by current employees. By prioritizing internal security measures and engaging the workforce in safeguarding company data, organizations can effectively reduce the likelihood of internal attacks disrupting their operations.
Implementing Robust Incident Response Plans
In the face of increasing cyber threats, having a robust incident response plan is essential for organizations aiming to protect their digital assets. An effective incident response plan enables businesses to quickly address and remediate cybersecurity incidents, minimizing potential damage. Organizations should regularly test and update their plans to respond to the evolving threat landscape. Chief Security Officers (CSOs) play a pivotal role in this process, ensuring that teams are prepared to act swiftly and efficiently in the event of a breach.
Additionally, organizations should consider incorporating advanced technologies such as threat intelligence and automation into their incident response strategies. By leveraging these tools, companies can identify potential threats early and respond proactively, rather than reacting after an incident has occurred. A well-structured incident response plan not only helps minimize losses but also instills confidence among stakeholders, clients, and employees, reinforcing the organization’s commitment to maintaining a secure environment.
The Intersection of Cybersecurity and Compliance
As the cyber threat landscape continues to evolve, so does the need for compliance with various regulations and standards. Organizations must understand that cybersecurity and compliance are intertwined; failure to adhere to compliance requirements can expose companies to both legal repercussions and increased vulnerability to cyber attacks. Chief Information Security Officers (CISOs) must stay informed about relevant regulations such as GDPR, CCPA, and HIPAA, and ensure that their cybersecurity protocols align accordingly.
Moreover, maintaining compliance necessitates a strong commitment to security across the organization. This includes regular audits, employee training, and continuous improvement of security measures. Companies that prioritize compliance are not only better positioned to protect themselves from breaches but also enhance their reputation in the marketplace. By fostering a culture of security compliance, organizations can significantly bolster their cybersecurity posture while simultaneously fulfilling regulatory obligations.
Secure Practices for Mobile Applications
As mobile applications become increasingly prevalent, ensuring their security is paramount for organizations. Cybercriminals often exploit vulnerabilities in mobile apps to gain unauthorized access to sensitive data or systems. Organizations must adhere to secure software development practices, implementing methods such as encryption, regular security testing, and user authentication to enhance the security of their mobile applications. Chief Information Security Officers (CISOs) should guide their teams in integrating security into every phase of the application development lifecycle.
Moreover, user education plays a critical role in mobile application security. Companies should inform users about best practices, such as downloading apps from trusted sources and being cautious with app permissions. Additionally, organizations should maintain a responsive approach to any vulnerability disclosures and updates to ensure that their mobile applications remain secure against evolving threats. By prioritizing the security of mobile applications, businesses can not only protect their data but also foster user trust and loyalty.
The Future of Cybersecurity in the Face of Growing Threats
As the digital landscape continues to evolve, the future of cybersecurity will be marked by increasingly sophisticated threats and new challenges for organizations. Emerging technologies, such as artificial intelligence and machine learning, promise to enhance security efforts, allowing for more effective threat detection and response. However, they also pose a dual challenge as cybercriminals may leverage the same technologies to launch more refined attacks. Therefore, businesses must not only adopt advanced technologies but also foster a proactive cybersecurity culture.
Looking ahead, organizations must prioritize ongoing investment in both technology and talent within the cybersecurity field. Attracting and retaining skilled professionals will be essential to keep pace with evolving threats. Moreover, encouraging diversity within cybersecurity roles, including more women in technology, can lead to innovative solutions and strategies that address the complex challenges ahead. By preparing for the future and adapting to changes, organizations can significantly bolster their cybersecurity defenses.
Frequently Asked Questions
What role do CISOs play in cybersecurity?
Chief Information Security Officers (CISOs) are responsible for developing and implementing security strategies to protect an organization’s information and technology assets. They oversee security protocols, manage risk assessments, and ensure compliance with regulations. With the increasing frequency of cyber threats, CISOs must stay ahead of potential vulnerabilities and adapt their strategies accordingly.
How are ransomware attacks affecting businesses today?
Ransomware attacks pose a significant threat to businesses, as they often lead to data breaches and financial losses. Attackers encrypt critical files and demand a ransom for their release. Companies are increasingly investing in cybersecurity measures, such as incident response systems and employee training, to mitigate the risk of falling victim to these attacks.
What are the best practices for ensuring cloud security?
To ensure cloud security, organizations should implement strong access controls, encrypt sensitive data, and regularly conduct security assessments. Additionally, maintaining a robust incident response plan and adopting a zero-trust security model can help organizations protect their cloud environments from cyber threats.
Why is it important to include women in technology roles within cybersecurity?
Including women in technology roles within cybersecurity is crucial as diverse teams bring a variety of perspectives and innovative solutions to tackle complex cyber threats. Women-led startups and initiatives have shown great promise in developing effective security measures, reinforcing the importance of diversity in creating a secure tech landscape.
What are the current trends in mitigating cyber threats?
Current trends in mitigating cyber threats include a focus on proactive cybersecurity measures, such as penetration testing and comprehensive employee training programs. With the rise of cloud computing and IoT devices, organizations are also adopting advanced threat detection technologies and enhancing their collaboration with cybersecurity professionals.
How can organizations prepare for the evolving cyber threat landscape?
Organizations can prepare for the evolving cyber threat landscape by continuously updating their security policies, investing in employee training, and deploying cutting-edge technologies. Regular risk assessments and collaboration with cybersecurity experts will also enable companies to adapt their strategies and improve their overall security posture.
What challenges do educational institutions face regarding cybersecurity?
Educational institutions face unique cybersecurity challenges, such as managing a wide range of devices and ensuring the security of sensitive student data. Implementing robust policies and training programs for both faculty and students is essential to protect against cyber threats and foster a culture of security awareness.
How can businesses address the cybersecurity talent shortage?
To address the cybersecurity talent shortage, businesses should invest in training and development programs for existing staff, actively recruit diverse talent, and create pathways for career advancement in cybersecurity roles. Partnerships with educational institutions can also help build a pipeline of qualified cybersecurity professionals.
| Key Point | Details |
|---|---|
| Current Cybersecurity Landscape | Cybersecurity is a pressing issue, with significant concern for Chief Information Security Officers (CISOs) due to the high frequency of attacks. |
| Frequency of Attacks | Approximately half a million cyber attacks occur every minute. |
| Emerging Threats | Predicted threats this year include innovative ransomware, IoT security issues, and internal threats. |
| Challenges in Cybersecurity | The growth of cloud services and new devices challenges traditional protection methods. |
| Proactive Approach | Organizations need to evaluate data protection needs and implement proactive threat prevention strategies. |
| The Role of Women in Tech | Women-led tech startups are making strides in cybersecurity, focusing on developing innovative security solutions. |
| CISO Recommendations | CISOs should focus on cloud security, mobile application development, and incident response systems. |
| Workforce Challenges | There is a lack of trained cybersecurity professionals, highlighting the need for skill development and training. |
| Educational Institutions | Security must be prioritized in educational institutions adopting cloud technology, including training and robust policies. |
Summary
Cybersecurity is rapidly evolving, and organizations must adapt to a myriad of threats and challenges. As the landscape changes, the importance of securing networks and data cannot be overstated. The insights from industry experts underscore the need for a proactive approach, emphasizing training, innovation, and collaboration. With women leading technological advancements in cybersecurity, the future looks promising as they bring fresh perspectives to mitigate risks effectively. Companies must focus on developing their cybersecurity strategies to navigate this dynamic environment successfully.